- Curl On Mac Failing While Dowling Ssl File Download
- Curl On Mac Failing While Dowling Ssl File Extension
- Curl On Mac Failing While Dowling Ssl File Opener
- Curl On Mac Failing While Dowling Ssl Files
CURL is a command line tool and library for transferring data with URLs. Curl.exe is the main executable for running cURL. This is not an essential process for Windows and can be disabled if known to create problems. CURL is a free, open-source application used in command lines and scripts to carry data over various protocols. The difference between @ and file get attached in the post as a file upload, while the makes a text field and gets the contents for that text field from a file. Example, to send your password file to the server, where 'password' is the name of the form-field to which /etc/passwd will be the input: curl -F password=@/etc.
Lonnie Posted: 9 Months Ago. To those who asked, and to those the author has failed to respond to apparently. The -k switch I believe is just going to ignore certificate errors I think the Author did this out of laziness. By adding -insecure and -k to the instructions, he makes sure it will work for more people. However, it also could be a risk because suddenly you're at risk for man in. CURL is a command line tool for transferring files with URL syntax, supporting FTP, FTPS, TFTP, HTTP, HTTPS, TELNET, DICT, FILE and LDAP. Curl supports SSL.
CA extract
Curl On Mac Failing While Dowling Ssl File Download
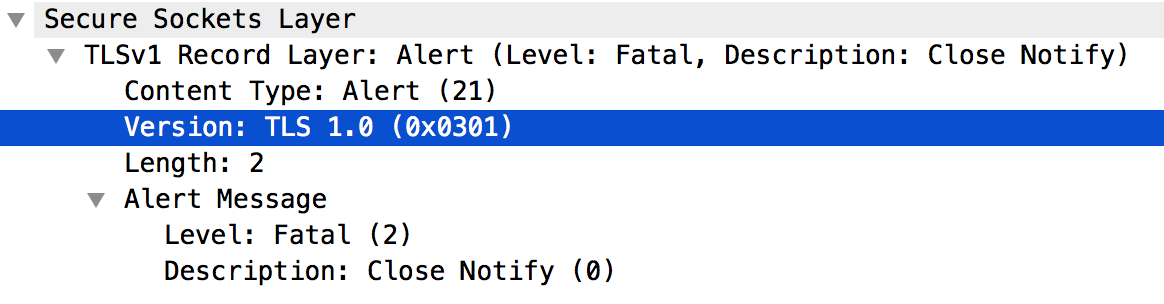
SSL is TLS
SSL is the old name. It is called TLS these days.
Native SSL
If libcurl was built with Schannel or Secure Transport support (the native SSLlibraries included in Windows and Mac OS X), then this does not apply toyou. Scroll down for details on how the OS-native engines handle SSLcertificates. If you're not sure, then run 'curl -V' and read the results. Ifthe version string says Schannel in it, then it was built with Schannelsupport.
It is about trust
This system is about trust. In your local CA certificate store you have certsfrom trusted Certificate Authorities that you then can use to verify that theserver certificates you see are valid. They're signed by one of the CAs youtrust.
Which CAs do you trust? You can decide to trust the same set of companies youroperating system trusts, or the set one of the known browsers trust. That'sbasically trust via someone else you trust. You should just be aware thatmodern operating systems and browsers are setup to trust hundreds ofcompanies and recent years several such CAs have been found untrustworthy.
Certificate Verification
libcurl performs peer SSL certificate verification by default. This is doneby using a CA certificate store that the SSL library can use to make sure thepeer's server certificate is valid.
If you communicate with HTTPS, FTPS or other TLS-using servers usingcertificates that are signed by CAs present in the store, you can be surethat the remote server really is the one it claims to be.
Curl On Mac Failing While Dowling Ssl File Extension
If the remote server uses a self-signed certificate, if you don't install a CAcert store, if the server uses a certificate signed by a CA that isn'tincluded in the store you use or if the remote host is an impostorimpersonating your favorite site, and you want to transfer files from thisserver, do one of the following:
Tell libcurl to not verify the peer. With libcurl you disable this with
curl_easy_setopt(curl, CURLOPT_SSL_VERIFYPEER, FALSE);With the curl command line tool, you disable this with -k/--insecure.
Get a CA certificate that can verify the remote server and use the properoption to point out this CA cert for verification when connecting. Forlibcurl hackers:
curl_easy_setopt(curl, CURLOPT_CAINFO, cacert);With the curl command line tool: --cacert [file]
Add the CA cert for your server to the existing default CA certificatestore. The default CA certificate store can be changed at compile time withthe following configure options:
--with-ca-bundle=FILE: use the specified file as CA certificate store. CAcertificates need to be concatenated in PEM format into this file.
--with-ca-path=PATH: use the specified path as CA certificate store. CAcertificates need to be stored as individual PEM files in this directory.You may need to run c_rehash after adding files there.
If neither of the two options is specified, configure will try to auto-detecta setting. It's also possible to explicitly not hardcode any default storebut rely on the built in default the crypto library may provide instead.You can achieve that by passing both --without-ca-bundle and--without-ca-path to the configure script.
If you use Internet Explorer, this is one way to get extract the CA certfor a particular server:
- View the certificate by double-clicking the padlock
- Find out where the CA certificate is kept (Certificate>Authority Information Access>URL)
- Get a copy of the crt file using curl
- Convert it from crt to PEM using the openssl tool:openssl x509 -inform DES -in yourdownloaded.crt -out outcert.pem -text
- Add the 'outcert.pem' to the CA certificate store or use it stand-aloneas described below.
If you use the 'openssl' tool, this is one way to get extract the CA certfor a particular server:
openssl s_client -showcerts -servername server -connect server:443 > cacert.pem- type 'quit', followed by the 'ENTER' key
- The certificate will have 'BEGIN CERTIFICATE' and 'END CERTIFICATE'markers.
- If you want to see the data in the certificate, you can do: 'opensslx509 -inform PEM -in certfile -text -out certdata' where certfile isthe cert you extracted from logfile. Look in certdata.
- If you want to trust the certificate, you can add it to your CAcertificate store or use it stand-alone as described. Just remember thatthe security is no better than the way you obtained the certificate.
If you're using the curl command line tool, you can specify your own CAcert file by setting the environment variable
CURL_CA_BUNDLEto the pathof your choice.If you're using the curl command line tool on Windows, curl will searchfor a CA cert file named 'curl-ca-bundle.crt' in these directories and inthis order:
- application's directory
- current working directory
- Windows System directory (e.g. C:windowssystem32)
- Windows Directory (e.g. C:windows)
- all directories along %PATH%
Get a better/different/newer CA cert bundle! One option is to extract theone a recent Firefox browser uses by running 'make ca-bundle' in the curlbuild tree root, or possibly download a version that was generated thisway for you: CA Extract
Neglecting to use one of the above methods when dealing with a server using acertificate that isn't signed by one of the certificates in the installed CAcertificate store, will cause SSL to report an error ('certificate verifyfailed') during the handshake and SSL will then refuse further communicationwith that server.
Certificate Verification with NSS
If libcurl was built with NSS support, then depending on the OS distribution,it is probably required to take some additional steps to use the system-wideCA cert db. RedHat ships with an additional module, libnsspem.so, whichenables NSS to read the OpenSSL PEM CA bundle. On openSUSE you can installp11-kit-nss-trust which makes NSS use the system wide CA certificate store. NSSalso has a new database format.
Starting with version 7.19.7, libcurl automatically adds the 'sql:' prefix tothe certdb directory (either the hardcoded default /etc/pki/nssdb or thedirectory configured with SSL_DIR environment variable). To check which certdbformat your distribution provides, examine the default certdb location:/etc/pki/nssdb; the new certdb format can be identified by the filenamescert9.db, key4.db, pkcs11.txt; filenames of older versions are cert8.db,key3.db, secmod.db.
Certificate Verification with Schannel and Secure Transport
Curl On Mac Failing While Dowling Ssl File Opener
If libcurl was built with Schannel (Microsoft's native TLS engine) or SecureTransport (Apple's native TLS engine) support, then libcurl will still performpeer certificate verification, but instead of using a CA cert bundle, it willuse the certificates that are built into the OS. These are the samecertificates that appear in the Internet Options control panel (under Windows)or Keychain Access application (under OS X). Any custom security rules forcertificates will be honored.
Schannel will run CRL checks on certificates unless peer verification isdisabled. Secure Transport on iOS will run OCSP checks on certificates unlesspeer verification is disabled. Secure Transport on OS X will run either OCSPor CRL checks on certificates if those features are enabled, and this behaviorcan be adjusted in the preferences of Keychain Access.
HTTPS proxy
Curl On Mac Failing While Dowling Ssl Files
Since version 7.52.0, curl can do HTTPS to the proxy separately from theconnection to the server. This TLS connection is handled separately from theserver connection so instead of --insecure and --cacert to control thecertificate verification, you use --proxy-insecure and --proxy-cacert.With these options, you make sure that the TLS connection and the trust of theproxy can be kept totally separate from the TLS connection to the server.